Account Security Options
Account owners can optionally enable several additional security features. If enabled, these features will affect all users in the account. Note that the account must have at least two owner status users to enable these settings.
Account owners can choose to enable PCI Mode for their account, which can be used for creating PCI compliant clusters. This will enable all security settings. Refer to our support article on PCI compliance for more information.
To modify your account’s security settings, click on the Settings Cog menu item in the top right of the console then Account Settings and then navigate to the Security tab.
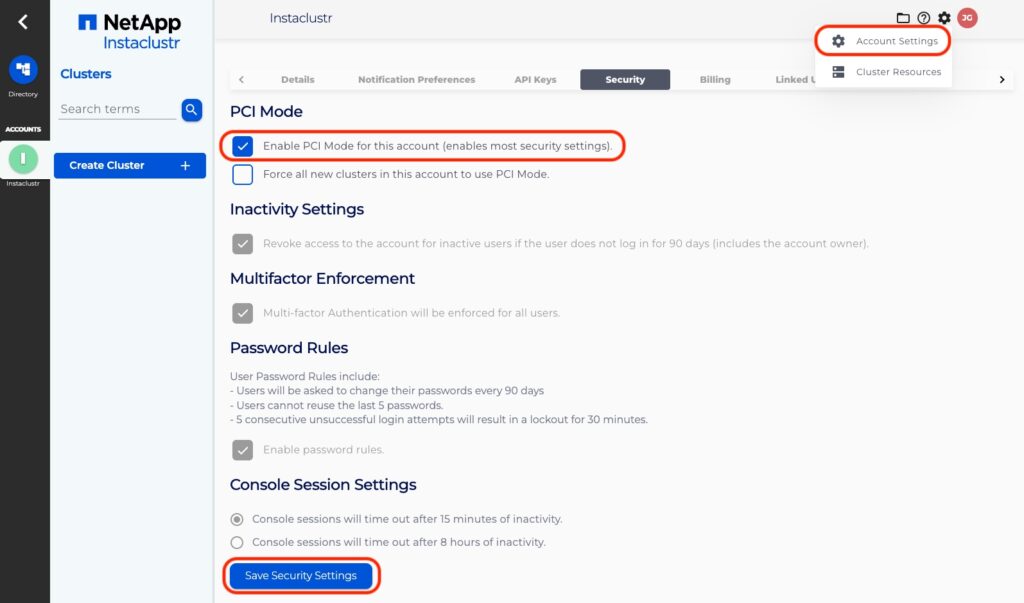
Screenshot
Table of Contents
PCI Compliance
Instaclustr provides PCI compliant services. As such, there are requirements that users must comply with in order to access and utilise our services with PCI Mode enabled. In order to learn more about PCI and the specific requirements, refer to our support article on PCI compliance.
In order for an account to be compliant with the PCI standards, it must satisfy all of the security options within the security tab.
If the PCI Mode setting is enabled, most of the other security settings will be set to their strictest level.
Additionally, you can select an option to only allow the creation of PCI Mode clusters in the future. Note that this will not affect any pre-existing clusters attached to this account.
To ensure compliance with PCI DSS v4.0, all user passwords must adhere to the following standards:
- Minimum length: Passwords must be at least 12 characters long.
- Character Composition:
- Must include at least one special character.
- Must include both uppercase and lowercase letters.
- Must include at least one numeric character.
Inactivity Settings
Revoke access to account for inactive users after 90 days of inactivity.
If this option is enabled, any user who has not logged on within 90 days will have access revoked for the accounts with this setting enabled. Users are notified through email 10 days and 1 day prior to account access revocation. Upon revoking a user’s account access, an account owner can re-invite the user back into the account through the console.
IMPORTANT: Owners can also have access for the account revoked if they do not log in. An account can end up with no owners this way. If this occurs, please contact us at [email protected] for assistance.
Multifactor Enforcement
Multi-factor authentication (MFA) will be enforced on all users in an account. Users who do not already have MFA enabled will be forced to set up the MFA requirements to access the account when they next log in.
Password Rules
Enabling this security feature will enforce the following:
- Users will be asked to change their password every 90 days
- Users cannot reuse the last 5 passwords
- 5 consecutive unsuccessful login attempts will result in a 30 minute lock-out
Five consecutive failed login attempts will result in a lockout for 30 minutes counting from the last failed login attempt. A user who is locked out this way will be prevented from logging in during this time.
The lockout period ends if:
- 30 minutes passes, or
- The account owner unlocks the user through a button on the console, or
- The user resets their own password through existing mechanisms (clicking a reset password link at the login form page or receiving a password reset email with a token).
Console Session Settings
To ensure security around unchecked console sessions, exposing provisioned clusters and sensitive information, users will be timed out after a period of inactivity and required to log in and re-authenticate.
Console sessions can be set to time out after 8 hours of inactivity (the default) or 15 minutes (for increased security)