Connect to an Apache Cassandra Cluster
Now that you’ve created a cluster, it’s time to connect your application to your new Cassandra cluster. Aside from setting your firewall rules, Instaclustr provides a few examples (customised to your cluster) for the wide selection of client libraries Cassandra supports to help you through this process.
- After your Cluster has finished provisioning, navigate to your Cluster Details page. All your nodes should be in a Running state with no errors listed. Some infrastructure providers allocate both public and private (data centre local) IP addresses to cluster nodes. If both are available, they will be listed with their respective nodes on this page.
We suggest that if your application is running within the same data centre as your cluster, you investigate configuring your client to connect to the private addresses. Please refer to your provider’s pricing documentation.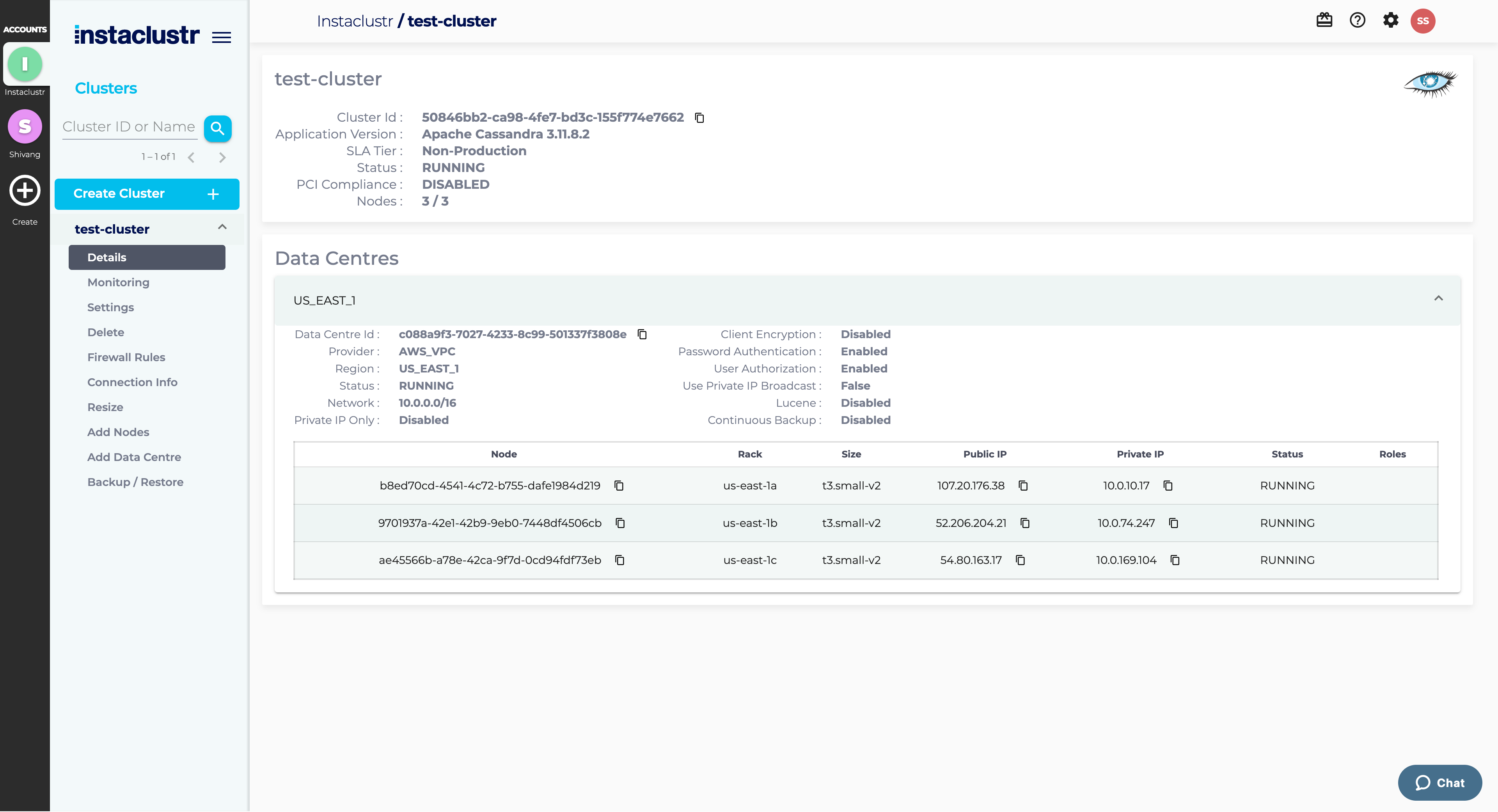
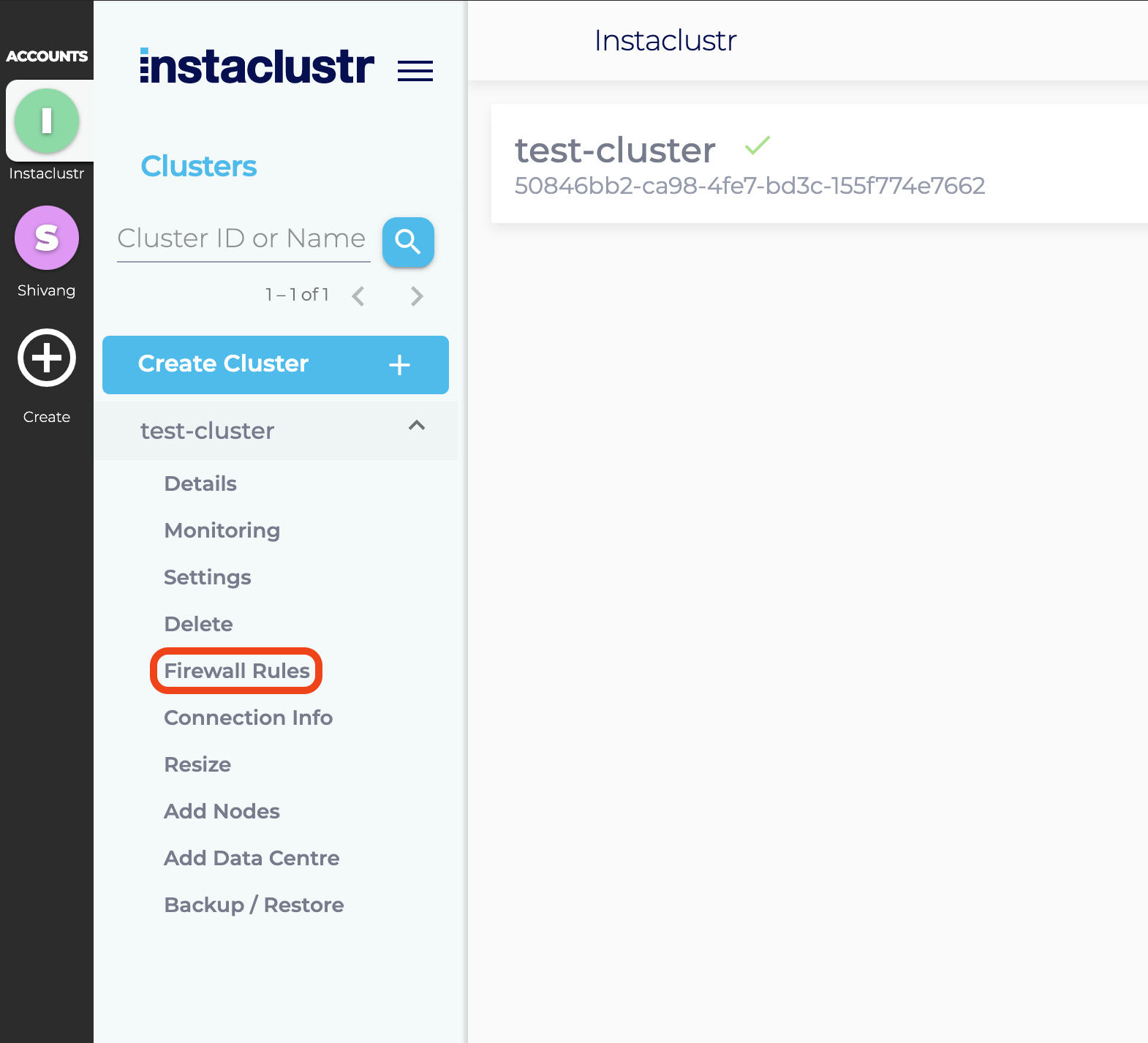
- Instaclustr manages the firewall permissions for the nodes in your cluster. Each cluster node only allows connections from one or more trusted IP addresses. You can add one or more trusted IP addresses to the cluster firewall by clicking on Firewall Rules from the sidebar.
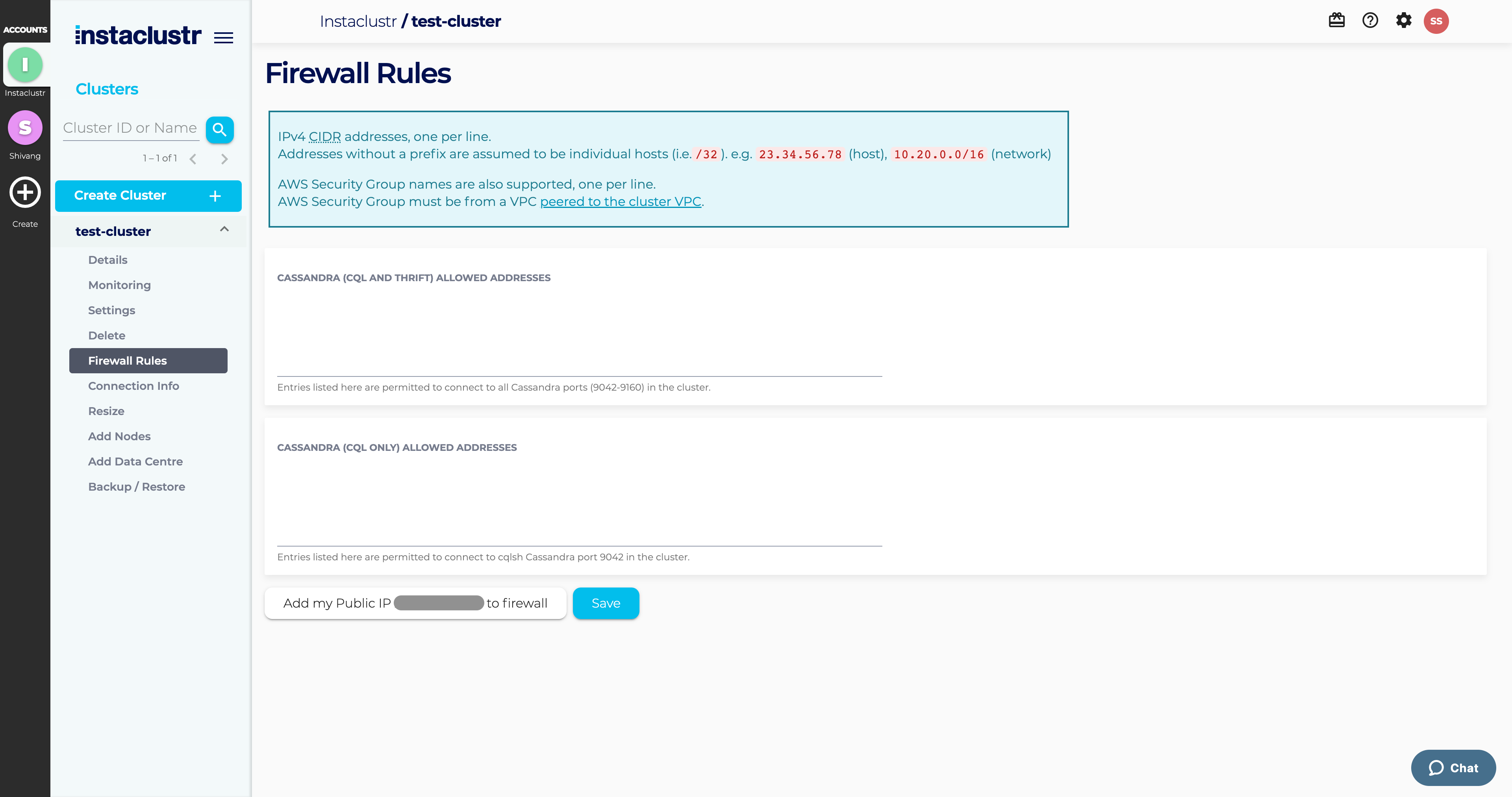
- Under the Firewall Rules section, enter any additional IP addresses you wish to trust to the Cassandra Allowed Addresses list. If your cluster is running on AWS and Cassandra clients are connecting using VPC peering, then you may also add one or more AWS security groups to the list. Click Add my Public IP to firewall to add your public IP address to the cluster firewall and then Save to save your changes.
- Instaclustr provides connection information and examples on the Connection Info page which can be accessed by navigating to the Connection Info tab from the sidebar.
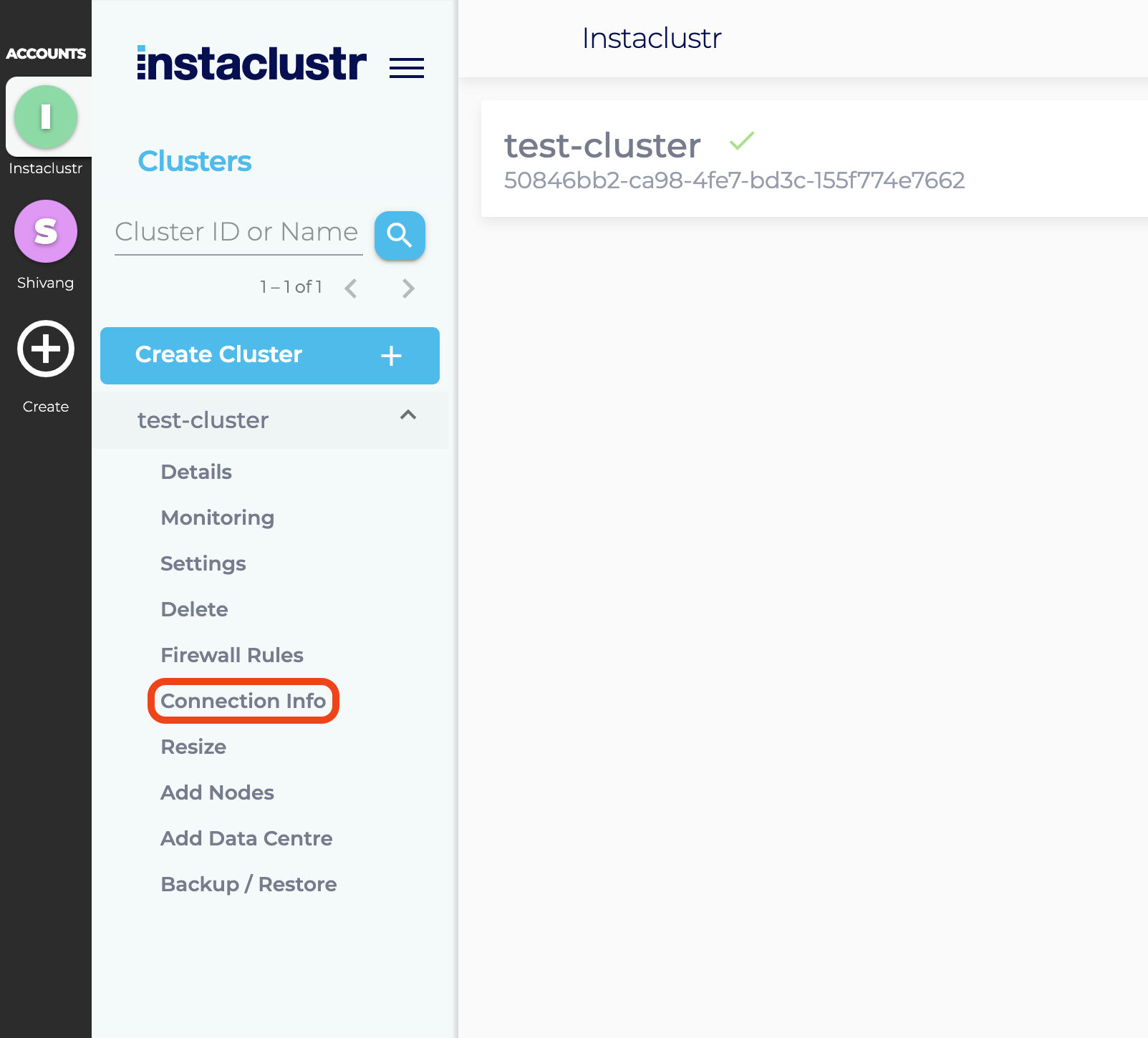
- The Connection Info page contains a list of your node addresses, authentication credentials to connect to your cluster and a few connection examples for popular clients Cassandra supports.
On the connection info page, you can access the Custom Subject Alternative names via the second tab Custom Subject Alternative Names where it’s possible to modify subject alternative names.
At this point, we provide custom examples for:- CQLSH
- Java
- Python
- Ruby
- We recommend reviewing the following support articles as a next step:
Cassandra has a large number of client libraries that support a wide set of languages.
- Java
- .NET
- C++
- Python
- Ruby
- PHP
- Node.js
- Go
- Clojure
- Scala
The Apache Cassandra project maintains a comprehensive list of clients for your language of choice.