Connect to a PrivateLink Cadence Cluster
Overview
This page describes the steps that need to be taken to connect clients in one VPC to a PrivateLink enabled Cadence cluster in another VPC. In short, customers need to create a security group, an endpoint with the endpoint service name of the created Cadence PrivateLink cluster, and a Route 53 record to the endpoint created.
Retrieve Required Cluster Connection Information
- Log into the console, click the created cluster and enter the Connection Info page.
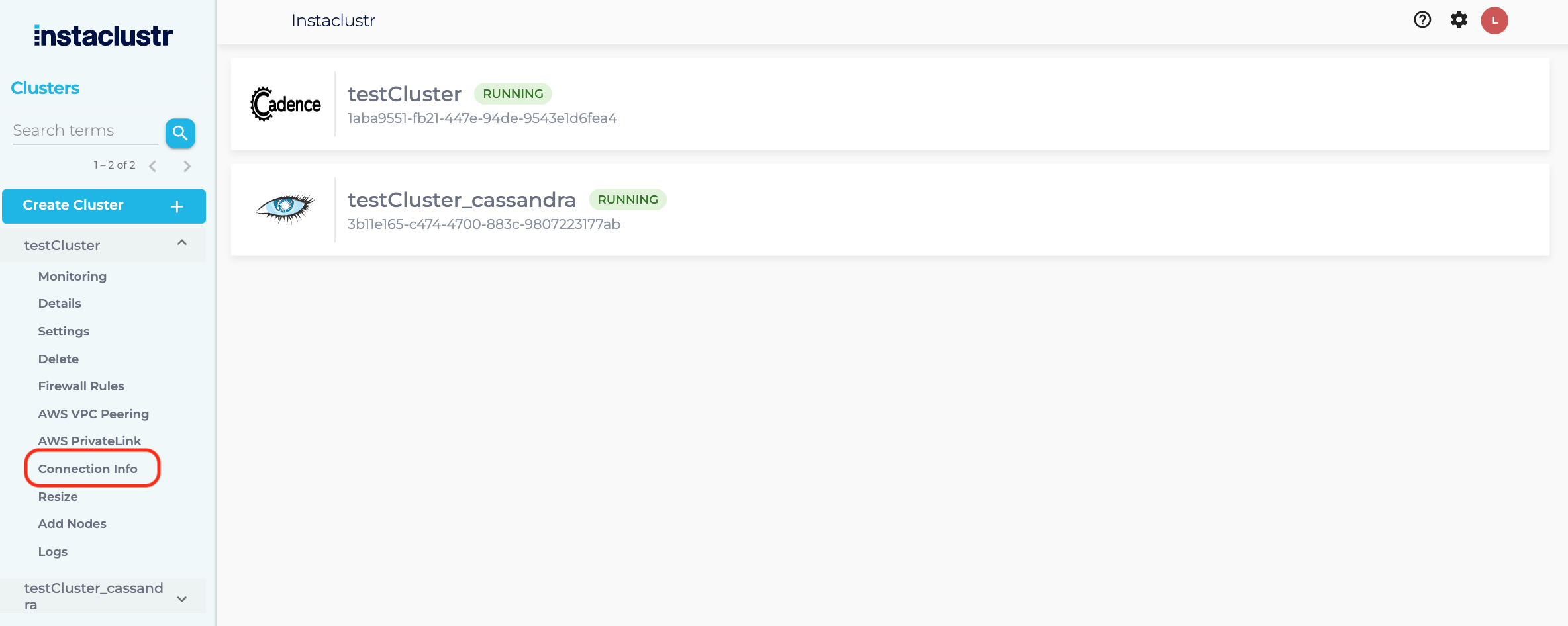
- The Connection Info page contains the specific connection details for PrivateLink. The endpoint created in the next section uses the endpoint service name shown below.
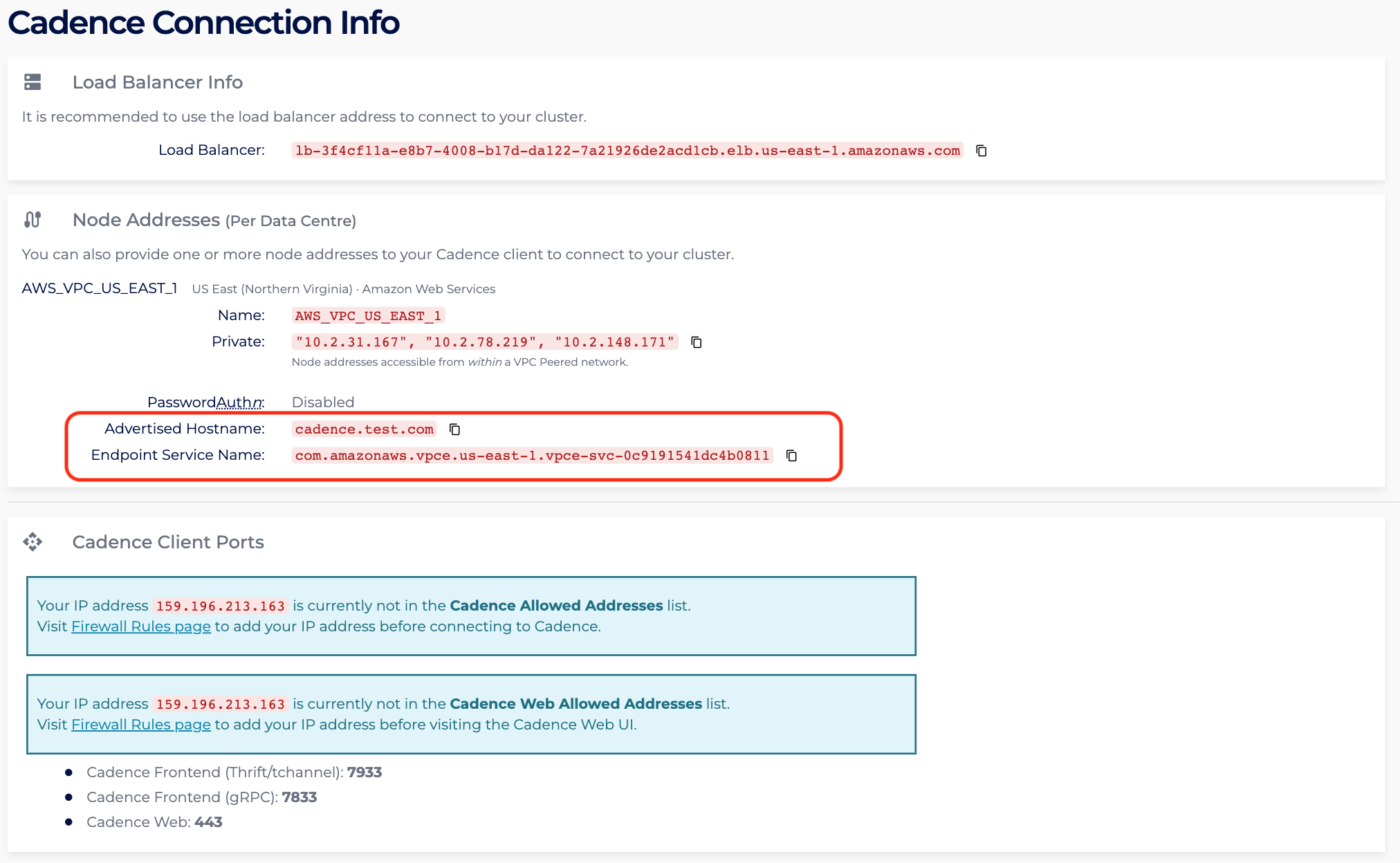
- In the Connection Info page, identify the region of the created PrivateLink Cadence cluster. For instance, the page shows the region is US_EAST_1, hence access to the AWS VPC Endpoint console in the US_EAST_1 region: https://us-east-1.console.aws.amazon.com/vpc/home?region=us-east-1#Endpoints:
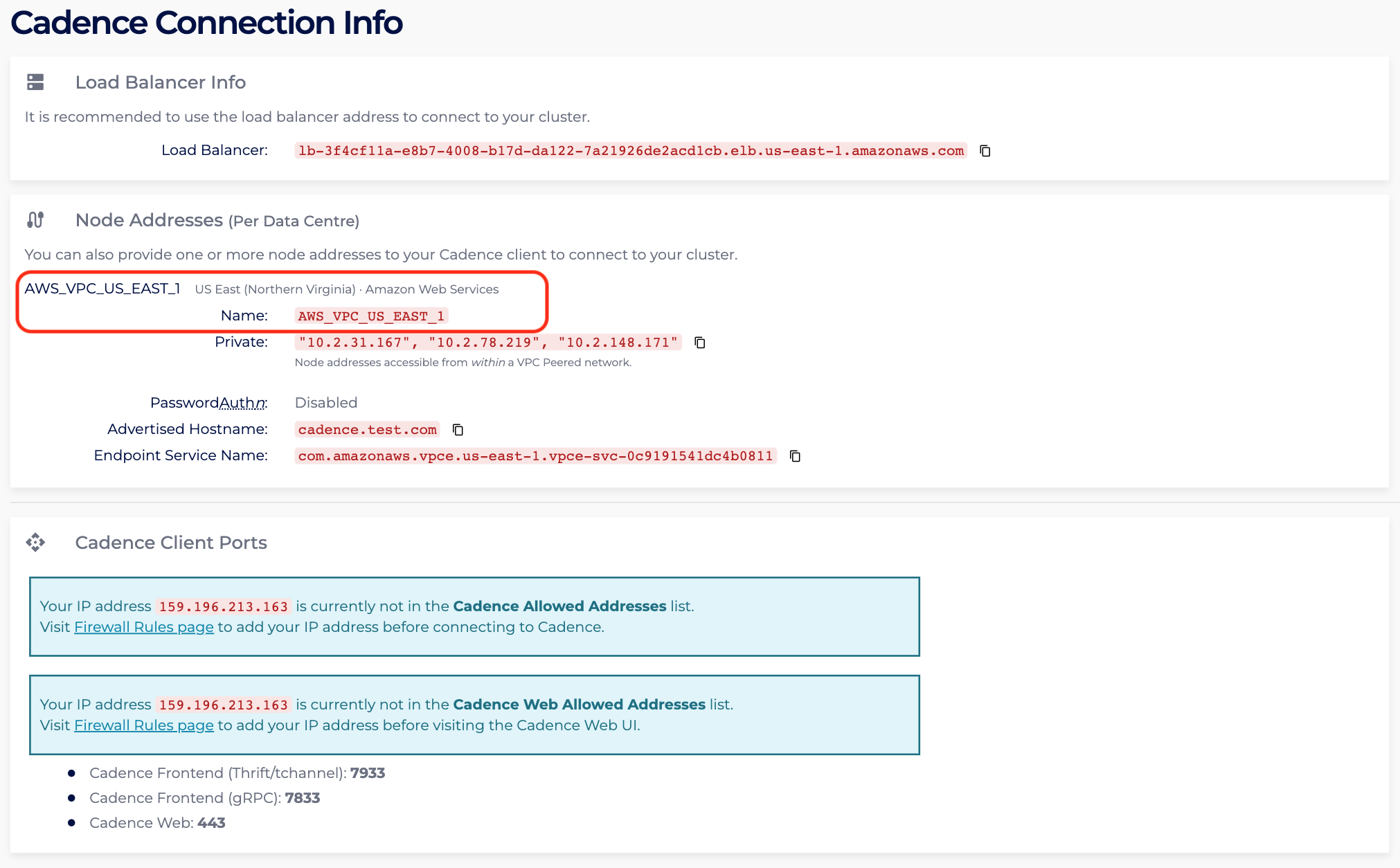
- If the PrivateLink Cadence cluster and client are in different AWS accounts, please ensure the AWS Principal of the client AWS account is added to allow cross-account access to the endpoint. For more info, please read Managing Principal ARNs of a PrivateLink Cadence Cluster.
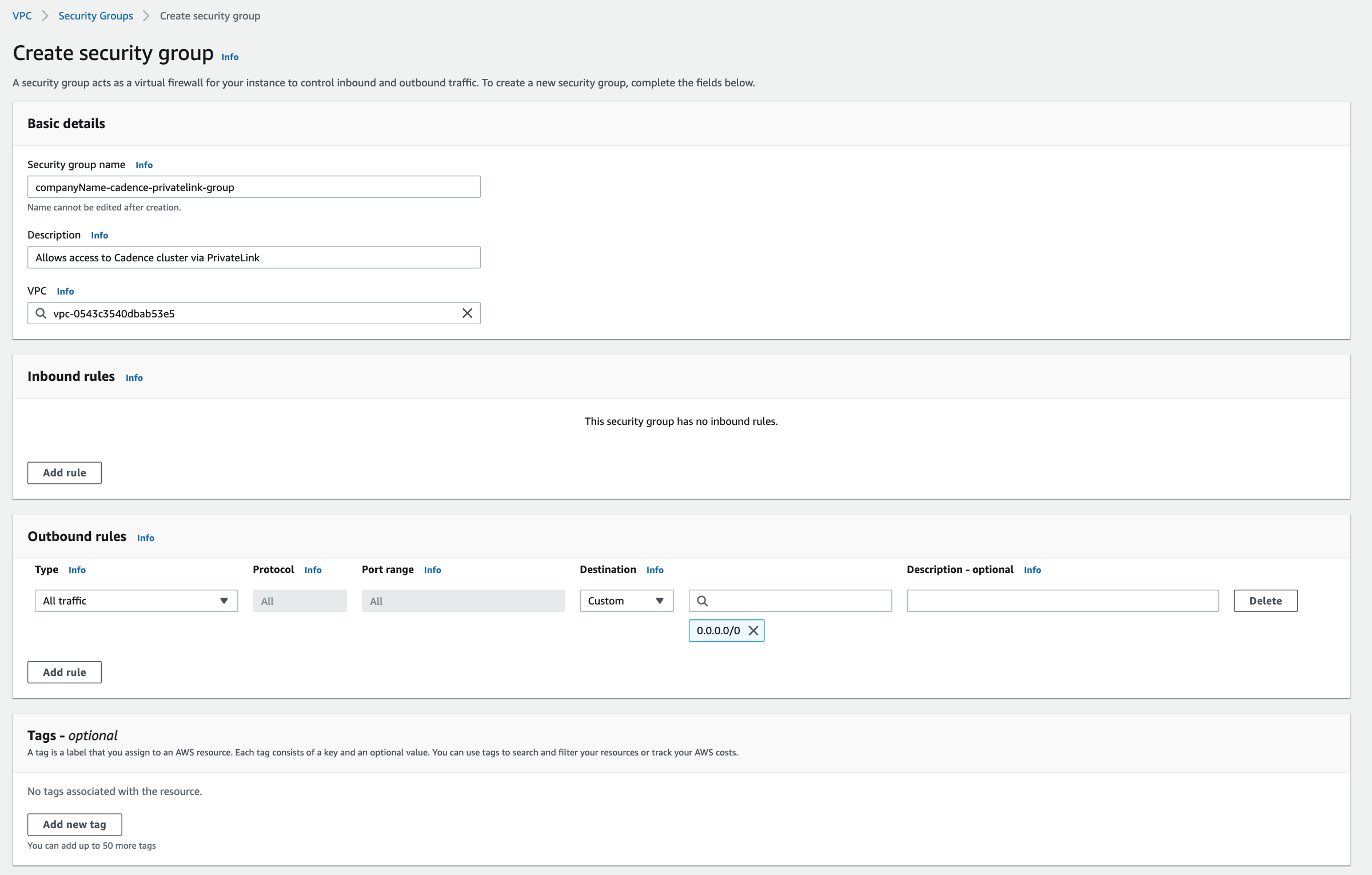
Create Endpoint Security Group
A security group is required to allow traffic from your VPC to the PrivateLink endpoint. Your Instaclustr provided Cadence cluster already has a security group applied to ensure the security of your cluster, but an Endpoint cannot be created without having an associated security group. Therefore the security group being created here can be as permissive or as strict as you require. These steps will outline the recommended security group configuration.
- In the AWS Console, select the appropriate region for your VPC and navigate to the Security Groups page.
- Click “Create security group”.
- Under the heading “Security group name”, enter a name for the security group. For example, “companyName-cadence-privatelink-group”. The name cannot be edited after creation, thus it is recommended to use a naming convention which allows easy identification of the PrivateLink endpoint and destination cluster it will be associated with.
- Under the heading “Description”, enter a short description of the security group. For example, “Allows access to Cadence cluster via PrivateLink”.
- Under the heading “VPC”, search for and select the VPC which will connect to the Cadence cluster via PrivateLink.
- Under the Inbound rules heading, click “Add rule”. The rules created here permit traffic outbound from your VPC, inbound to the Cadence cluster over PrivateLink.
- Select Custom TCP in the “Type” field. Enter 7933, 7833 and 443 in the “Port range” field (n.b. Port 7933 and 7833 are the Cadence Frontend Service listener port for tChannel/gRPC. When connecting via PrivateLink, these ports are load balanced between all Cadence nodes in your cluster. Port 443 is the Cadence Web listener port, this port will direct to Cadence Web node. All these three ports will not change, and can be verified on your Cadence cluster’s Connection Info page.) Select Custom in the “Source” field, then enter the CIDR of the subnet you will be connecting to the PrivateLink endpoint from (ie. the CIDR within which your EC2 Instance resides). Optionally, add a description in the Description field.
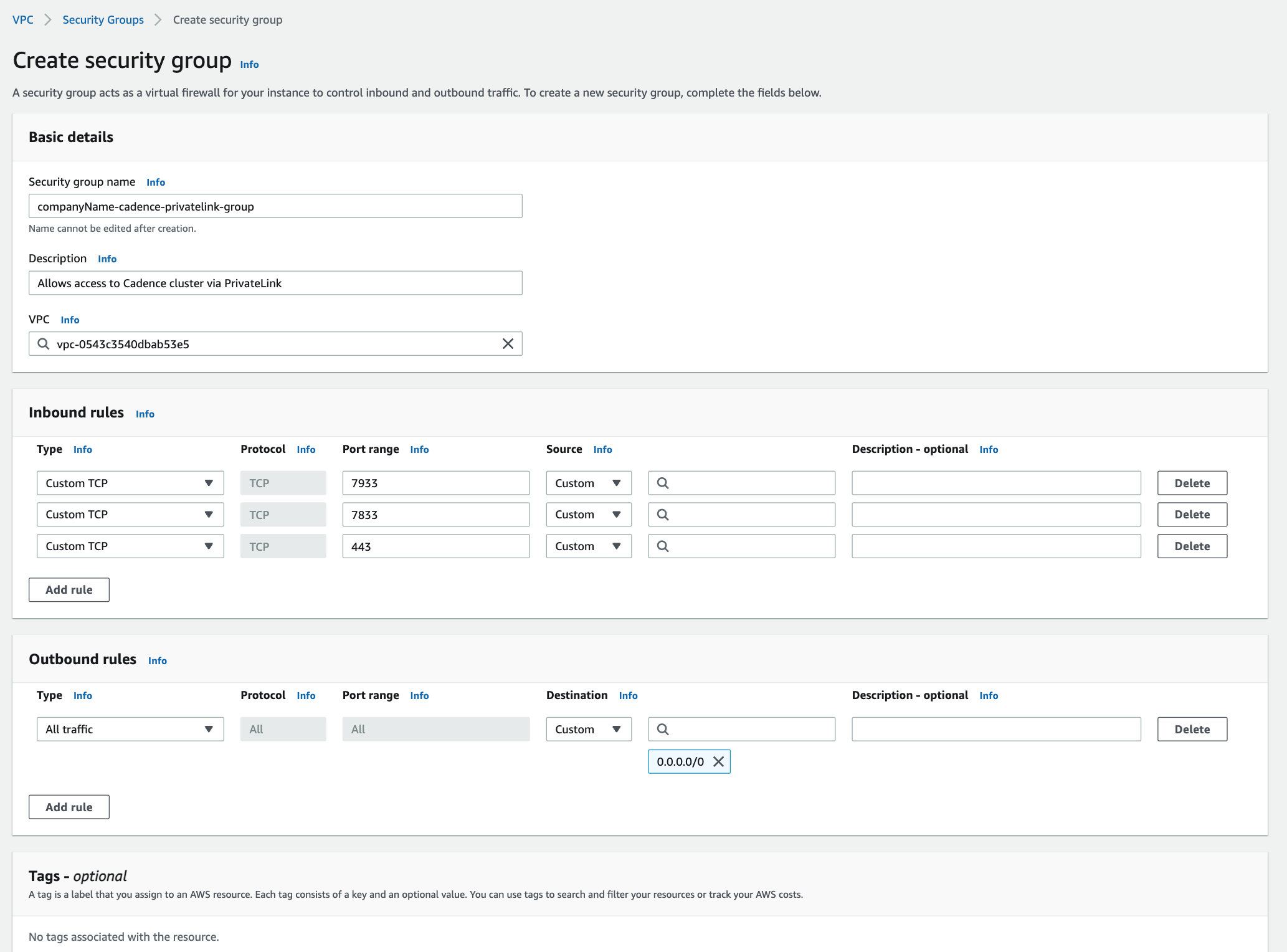
- Click “Create security group”, the security group should be created successfully. Take note of the security group name, as it will be required when creating the Endpoint in the following steps.
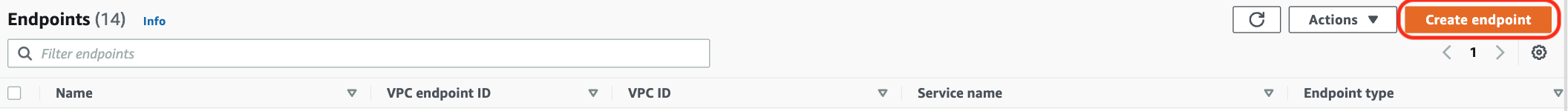
Create Endpoint and Route 53 Record
- On the AWS VPC Endpoint Console page, click “Create endpoint”.
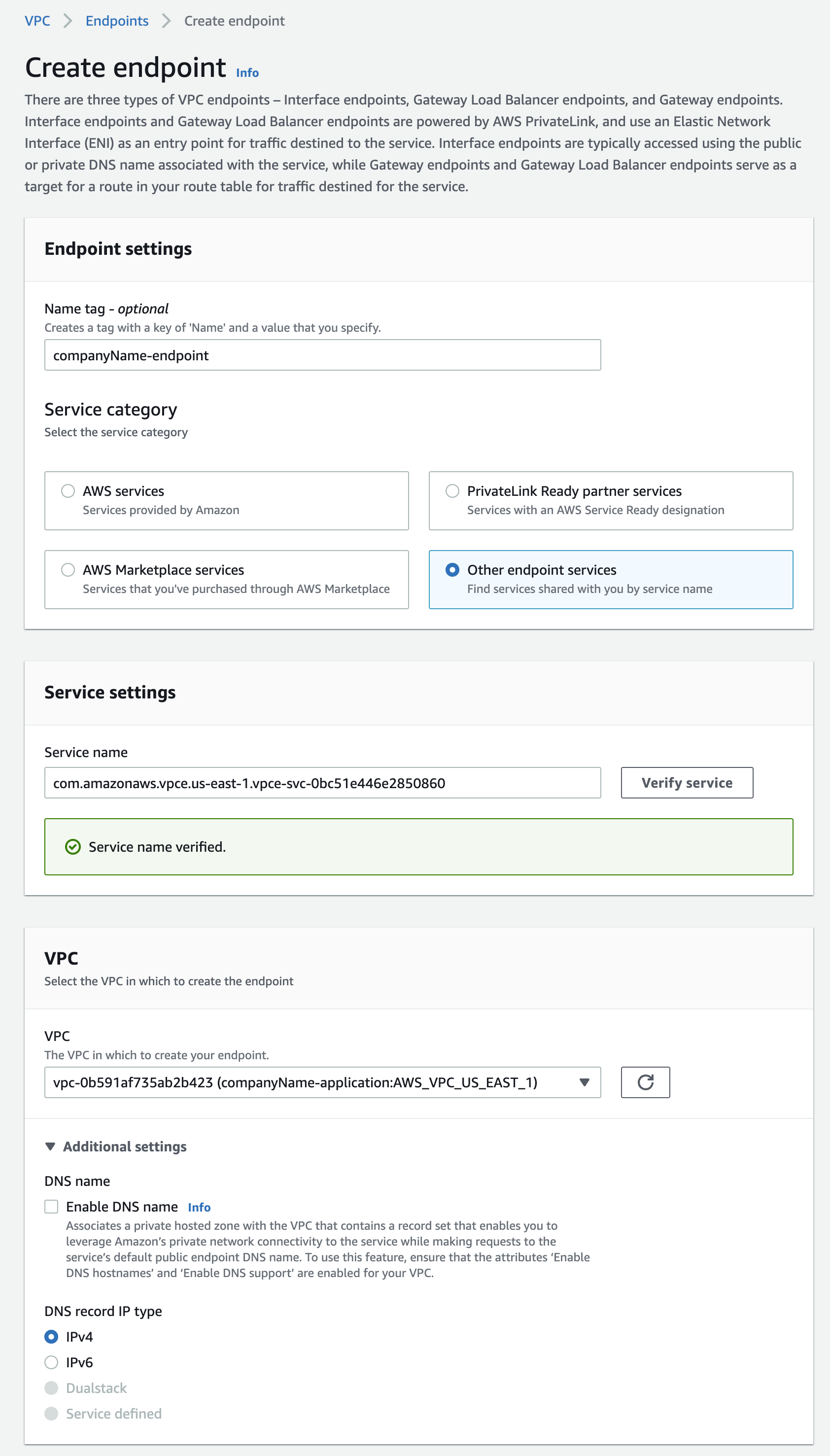
- On the creation page under “Service category”, select “Other endpoint services”
- In “Service Settings”, paste the endpoint service name from step 2 to the “Service name” field. Click “Verify service” and a green box will appear.
- For “VPC”, select the client’s VPC that will connect to the PrivateLink Cadence cluster. Note, the VPC of the client and PrivateLink Cadence cluster should be in the same region as we do not support inter-region access via PrivateLink.
- The configuration would then be as follows.
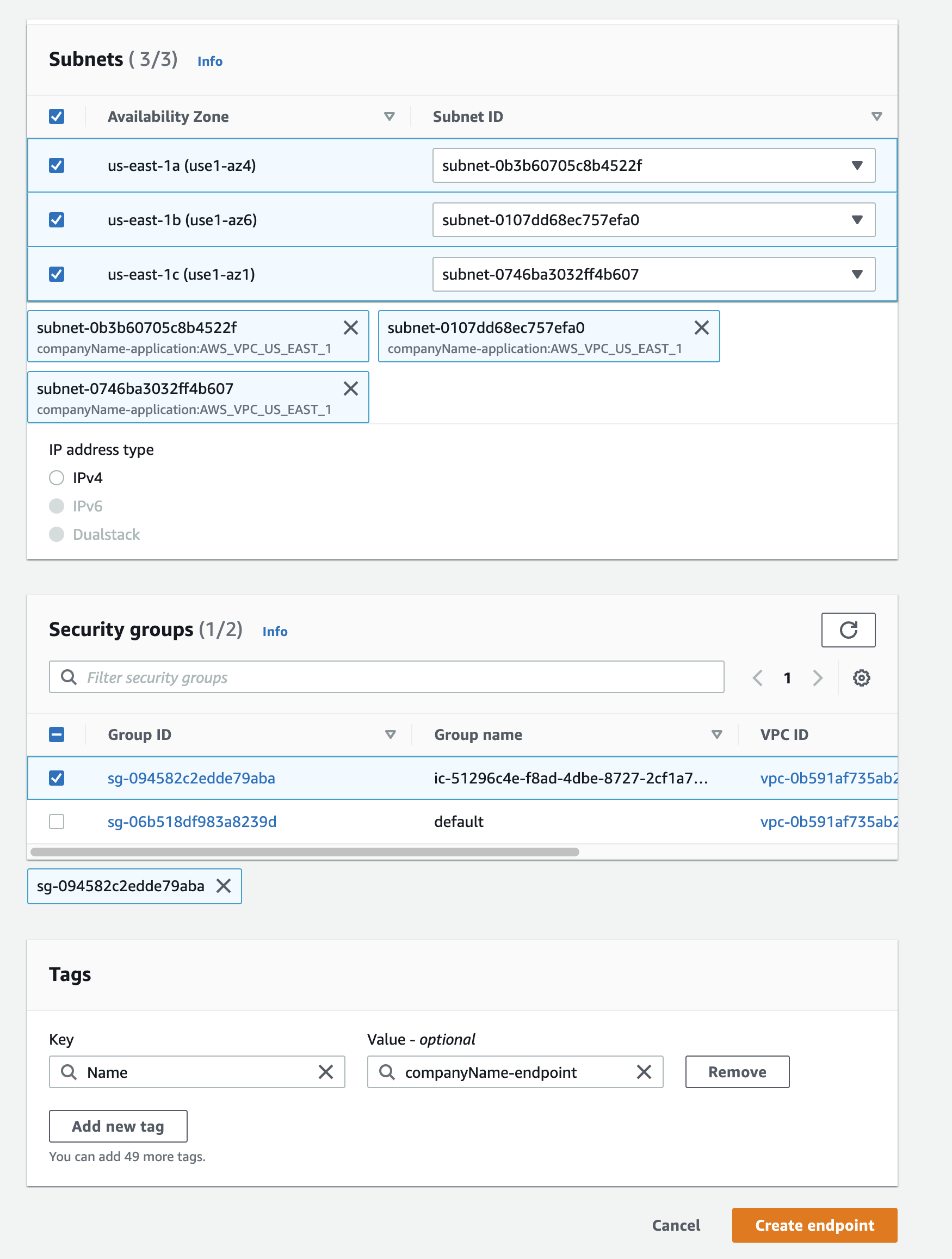
- For “Subnets”, please select one “Subnet ID” for each “Availability Zone”. Please note that we recommend that your clients (producers and consumers) be located in separate availability zones to support high availability should any one availability zone be unreachable.
- Select the security group that you created earlier. You will get the following configurations. Once done, click “Create endpoint”.
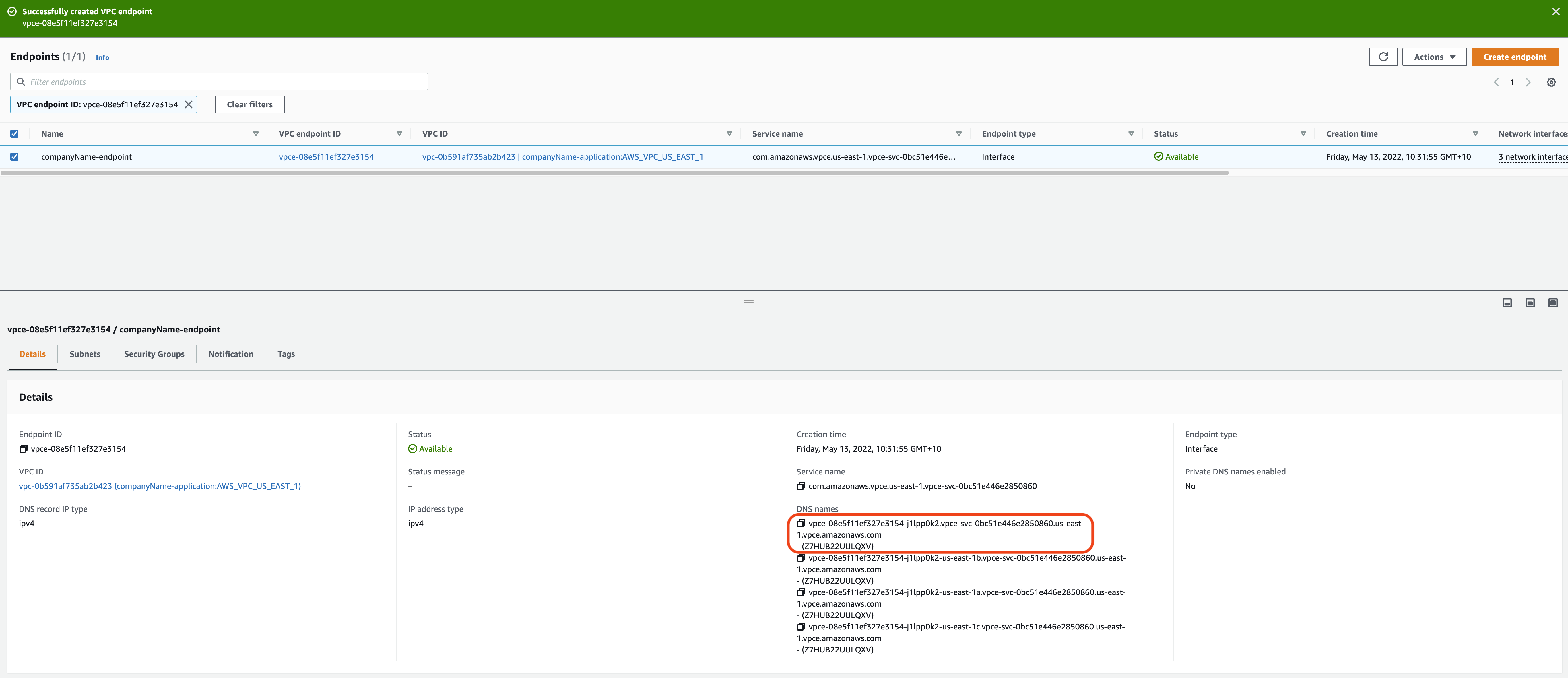
- You will be redirected to the main VPC endpoint page which will specifically show the created endpoint. Once the Status of the endpoint reaches Available, copy the first DNS under the “DNS names”.
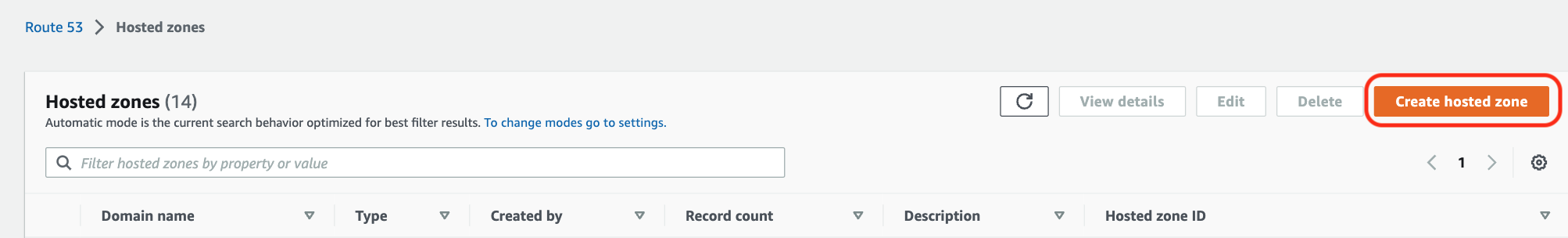
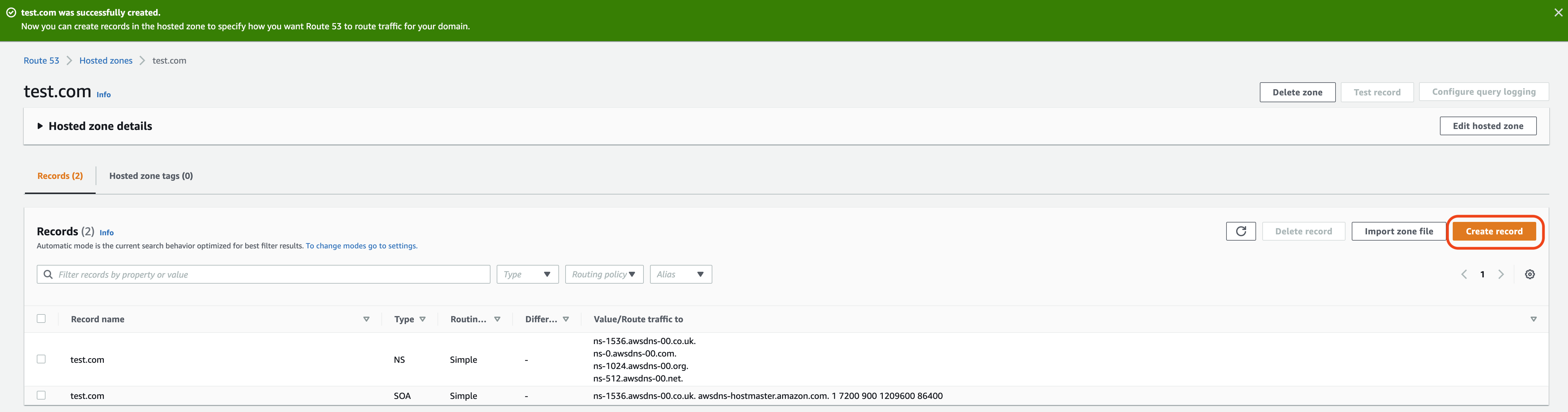
- Head to the Route 53 record home page, enter Hosted Zone and select “Create hosted zones”. https://us-east-1.console.aws.amazon.com/route53/v2/hostedzones?region=us-east-1#
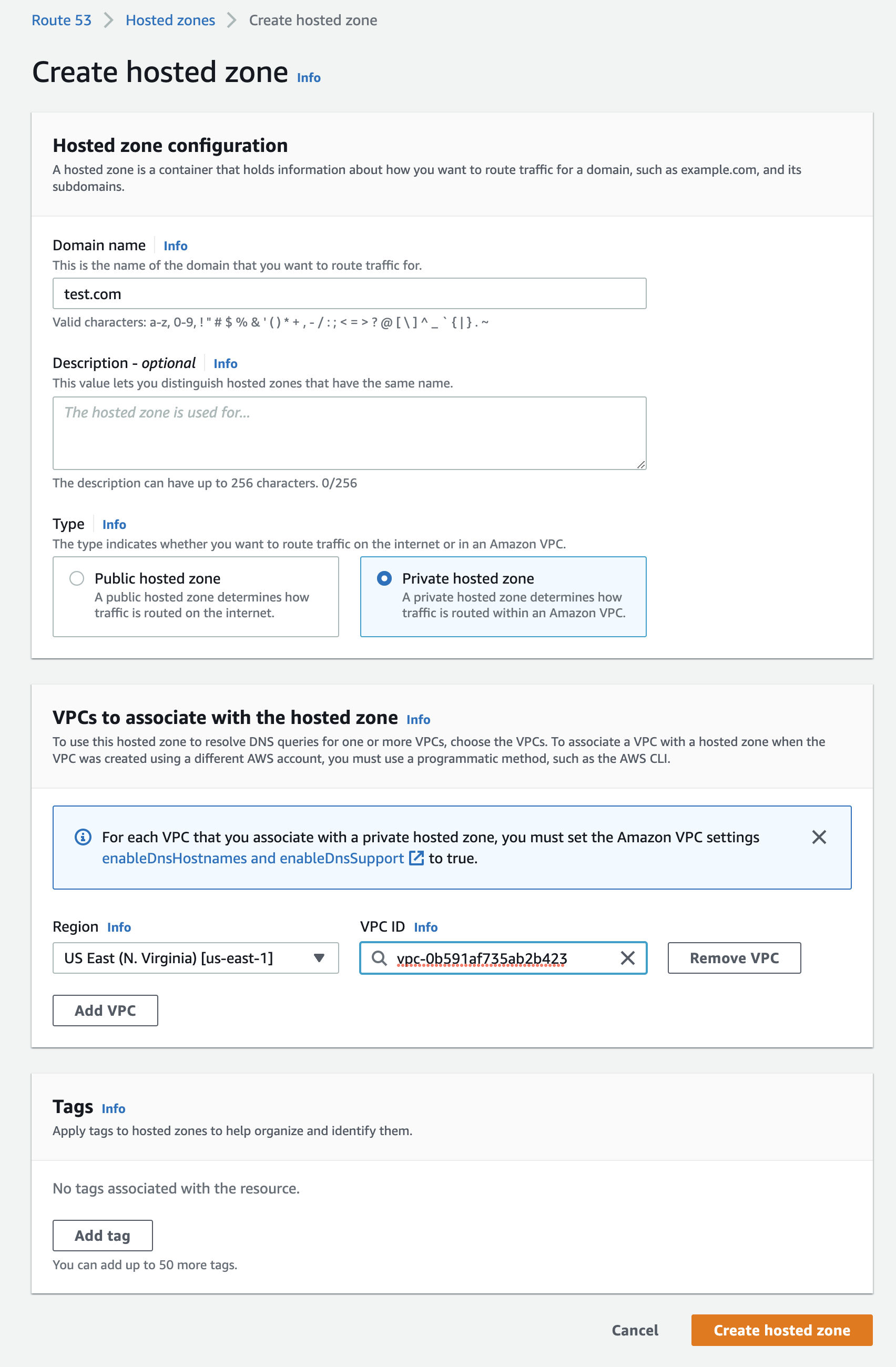
- Find the “URL” in Retrieve Required Cluster Connection Information step 2. Under “Advertised Hostname”, enter the “URL” without the first part of the hostname into “Domain name”. For example for cadence.test.com, enter test.com.
- Select “Private hosted zone” as “Type”.
- Select the corresponding region and VPC of the client used in step 4.
- Ensure you have the following configurations, click “Create hosted zone”.
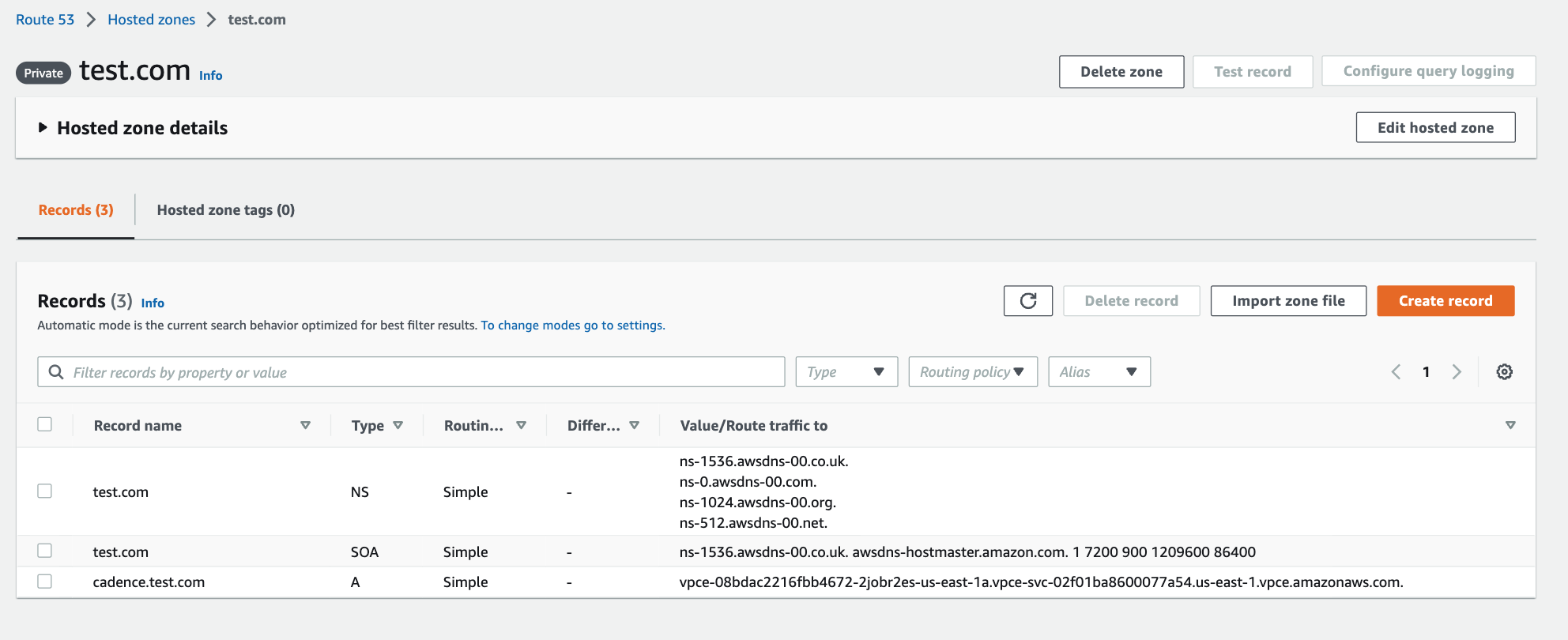
- You will be redirected to the created private hosted zone.
- Select “Create record”.
- Under “Record name”, place the rest of the “URL” from step 2. For instance, the “URL” is cadence.test.com and we entered test.com in step 13. Thus the remaining URL to be entered is cadence.
- Click the toggle “Alias” and select “Alias to VPC endpoint” from the dropdown box.
- Select the same region as the one in step 3 in the next dropdown box.
- In the last field, paste the endpoint DNS name from step 8.
- The resulting configuration is as follows.
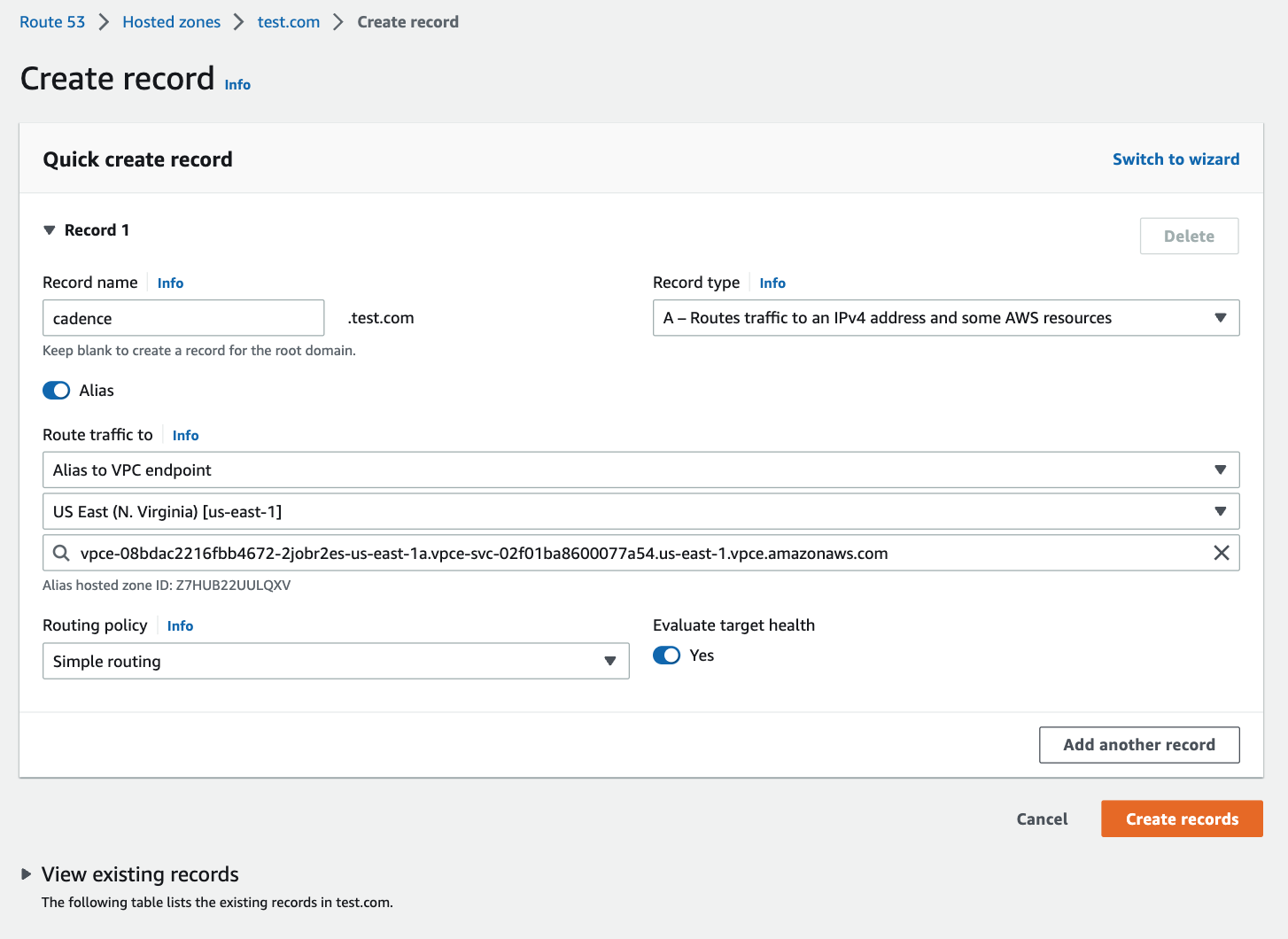
- The newly created record will be in the hosted zone. You can now connect to the cluster with cadence.test.com:7933(Thrift/tchannel) or cadence.test.com:7833(gRPC).